Nowadays, it’s normal to have more than two accounts, aside from your email. There are bank accounts, file sharing websites, online storage, and numerous social media accounts.
Keeping your information safe can be challenging. Sure, you can choose a complicated password. But what if you have more than 10 accounts? If you use the same password more than once, your security is already compromised.
So here’s where two-factor authentication or 2FA comes in.
What is 2-factor authentication?
Also called as multi-factor authentication, dual-factor authentication, or 2-step verification, two-factor authentication is meant to provide an additional layer of protection against cybercrime.
The usual authentication process involves a username and password. In 2FA, the user will be required one more step before being granted access to the account. This is normally done via a unique code sent as an SMS, or a fingerprint scan. But there are other ways, depending on the level of security a person wants to have.
Types of Authentication Factors

Today, experts recognize three main authentication factors:
- something you know (e.g. password)
- something you have (e.g. mobile phone)
- something you are (e.g. fingerprint)
‘Something you know’ is referred to as the knowledge factor. Think of it as a secret, a thing only you – and your account – should be aware of. Aside from passwords, PINS and security questions also fall into this category.
‘Something you have’ is known as a possession factor. Financial and government institutions typically make use of this element. This can come in the form of ID cards, security tokens, mobile devices, or a smartphone app.
‘Something you are’ is also called an inherence factor or a biometric factor. Perhaps the most unique of all, as this can range from your fingerprint, to your keystroke dynamics, as well as voice recognition. Apple devices and Windows Hello uses biometric factors to secure their users’ information by way of retina and facial recognition.
Two other less familiar authentication factors are location and time. For a location factor, either authentication attempts are limited to specific devices in a single location, OR it uses the individual’s Internet Protocol (IP) address. In time factor, a person must login under a restricted time period and losses their access if they leave the window.
Two-factor authentication uses two of any of these authentication elements. The most common is a combination of a knowledge factor (e.g. password) and either a possession (code through SMS) or biometric (fingerprint or facial recognition) factor.
Importance of 2-Factor Authentication
While passwords have helped keep our accounts safe for years, tech and security experts argue over its obvious vulnerabilities.
Here are a few reasons why that security protocol isn’t enough:
- People make simple passwords. You’ll be surprised at some common ones in use today, including: ‘111111’, ‘123456’, ‘qwerty’, and believe it or not, ‘password’.
- Users become complacent with time. The recommended security measure is changing your password every three months, and using a different one each time. But individuals hardly do that in reality.
- Having too many accounts with recycled passwords. This is in connection with point #2. Just because you didn’t experience phishing or hacking, doesn’t mean you never will. Also, if a family member, co-worker, or friend’s account becomes compromised, it’s possible that your account will be too, since you’re connected to them.
Let’s make it a point to teach others about online security and authentication. If you know of a friend or loved one who isn’t using 2FA yet, teach them how.
How does it work?

Enabling dual-factor authentication gives users two prompts – instead of just one – during login.
The first step will typically ask for a username/email and password. For websites that won’t ask for these, they might generate unique security keys instead. Once the user successfully inputs their data, the next login step begins.
For the second authentication component, it could take the form of possession (SMS) or biometric (facial or fingerprint recognition) factors. For those using security keys such as Yubikey, a physical USB gadget, all you need to do is plug it on your device, tap it, and wait for the validation.
Once both steps are successful, the user can now access the website or app.
Here are some examples of how to setup dual-factor authentication on commonly used online services:
For Amazon
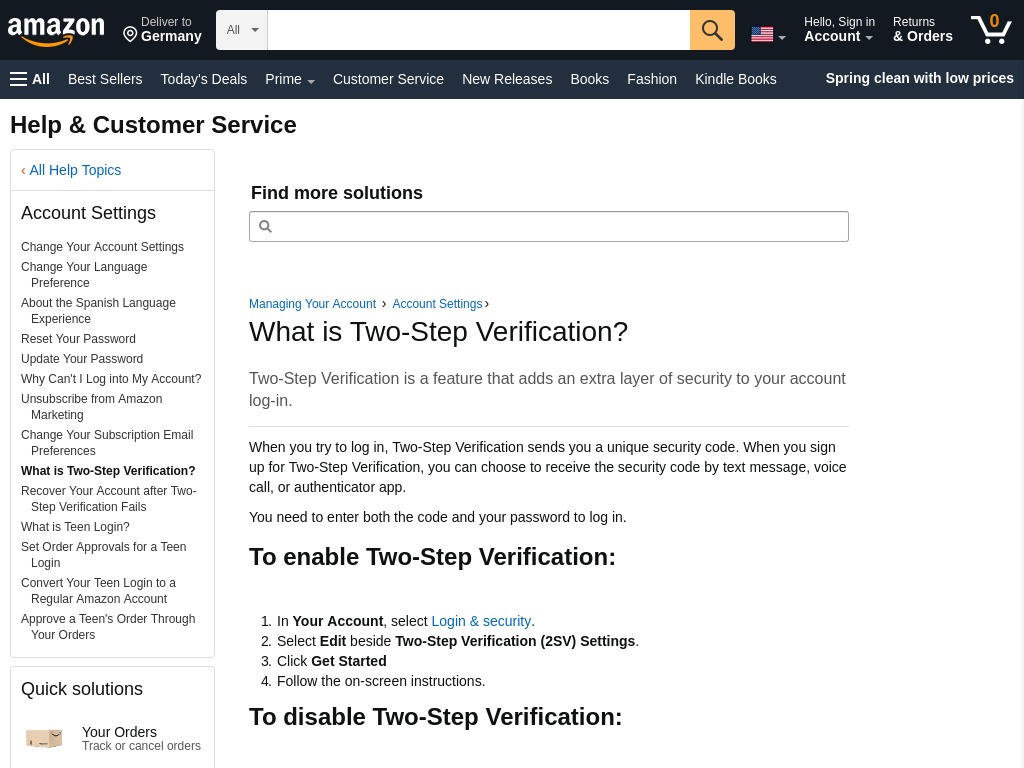
For avid Amazon users, this can help you secure various products from this multinational technology company, such as your Audible and Amazon Prime.
- Go to your Account, select Login & security.
- Choose Edit beside Two-Step Verification (2SV) Settings.
- Click ‘Get Started’.
- Follow the on-screen instructions.
For Apple ID

For iOS or Mac users, this is a must! Aside from getting added defense for your devices, you also need this to secure your iCloud storage, and your memberships to Apple Music and Apple TV+.
- Go to Settings > [your name] > Password & Security.
- Tap ‘Turn On Two-Factor Authentication’.
- Choose Continue.
- Enter the phone number where you want to get verification codes when you sign in. You can choose to receive the codes via SMS or an automated phone call.
- Tap Next.
- Enter the verification code to confirm your phone number and turn on two-factor authentication.
*Please note that you may be asked for additional security questions. Please visit the link above for more details.
For Facebook
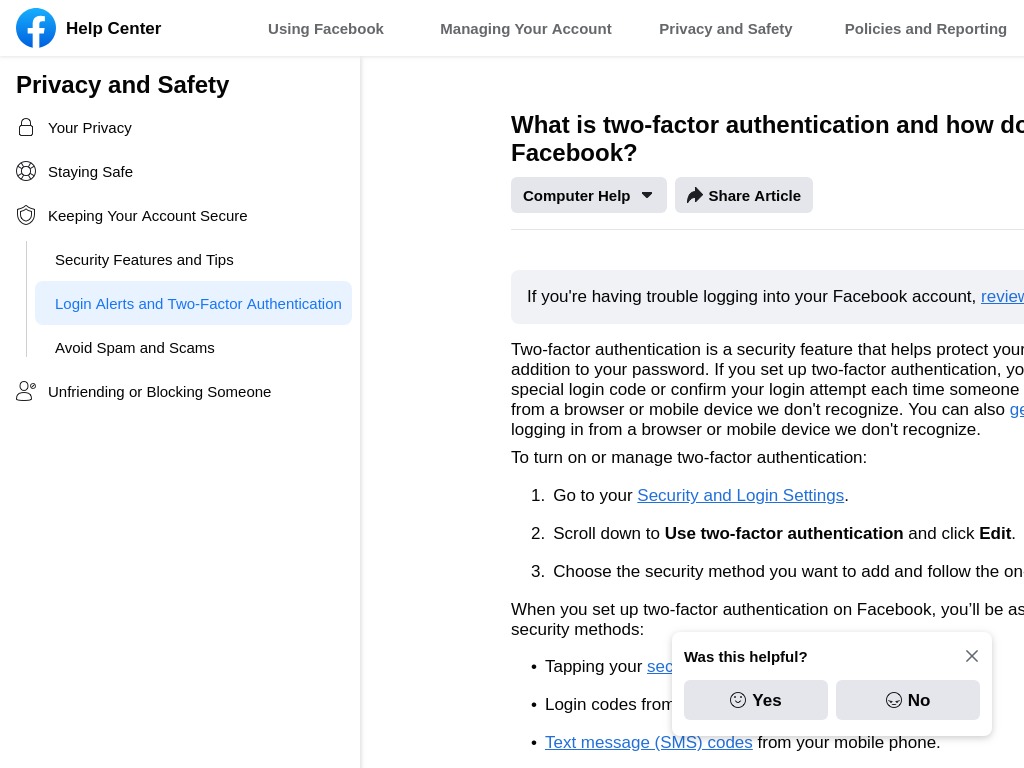
As one the world’s most popular social media, it’s vital that you secure your personal details here by way of 2FA. Here’s how:
- On your account, go to Security and Login Settings.
- Scroll down to Use two-factor authentication.
- Click Edit.
- Choose the security method you want to add, and follow the on-screen instructions.
For Google
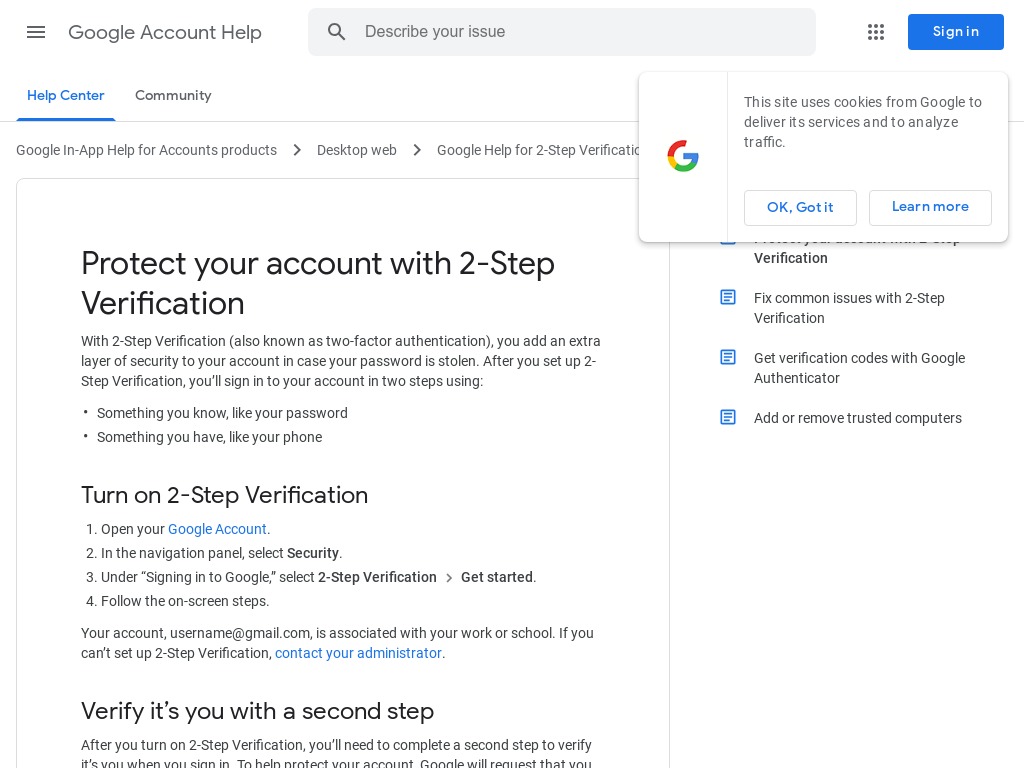
Many people nowadays use various Google products, from Gmail, Google Drive, Maps, YouTube, to Calendar, Photos, and Analytics. The last thing you want is to wake up and realize you can’t login to your accounts!
- Open your Google Account.
- In the navigation panel, select Security.
- Under ‘Signing in to Google’, select 2-Step Verification and then Get started.
- Follow the on-screen steps.
Is it 100 percent secure?

Staying safe today isn’t easy. While two-factor authentication improves your protection, it’s not perfect.
For one, hackers are ingenious at coming up for ways to bypass the system. A good example would be the hack on Jack Dorsey’s Twitter account in 2019. The bad guys obtained access via a SIM swap attack. The usual modus is to convince your carrier to switch numbers to the ones they have, thereby bypassing the 2FA process altogether.
Second, one component of your two-factor authentication may be weak – as in the case of a flawed account recovery scheme. This is what happened in 2012, when the Gmail account of Matthew Prince, CEO of CloudFlare, was compromised.
That means you shouldn’t keep your guard down. Using 2FA is a smart step towards better security online. However, one must still practice great care in protecting personal information.
Here are a couple of reminders:
- Use a strong password that employs a mix of upper- and lowercase letters, special characters, and numbers.
- Avoid easy words, numbers, or phrases like your birthday, last name, or your nickname. Change your password as often as every three months.
- Avoid connecting to public WiFi as much as possible.
- Dispose of personal data securely. For instance, don’t simply throw away your company ID or billing statements in the trash. Shred them to render them unusable or unreadable.
How about you? Do YOU use two-factor authentication?

